Ansible is an excellent tool for automating procedures across multiple machines. To do this, it uses multiple SSH connections to predefined hosts to perform remote tasks. These tasks can be anything from a simple SSH command to a complex automation processes defined by an Ansible playbook. Playbooks are YAML files that define multiple procedures across several hosts, making it a powerful tool, but one that needs to be protected. Most importantly, the SSH credentials controlling access and the playbook access must be controlled, monitored and secured.
CyberArk provides several integrations with Ansible to help secure it. Our mission is to help you perform your daily work as securely and seamlessly as possible.
Discover and Remove Secrets from Ansible Playbooks
Make sure that there are absolutely no hard-coded credentials in any of your Ansible playbooks. Ansible Playbooks often contain credentials that access target services while performing complex tasks. The best practice is to store these credentials in a secure vault like CyberArk Conjur and then use its integration with Ansible to retrieve them as needed. It is important to store these credentials securely because Ansible Playbooks are often checked into source code repositories like GitHub, allowing the public or larger development organizations to view the secrets, thus exposing these powerful access credentials to a much larger audience than you perhaps intended.
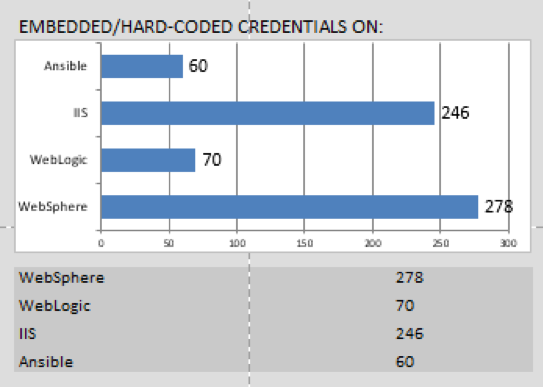
Even if the playbook was originally written with no credentials in it, someone can still add them later. For this reason, CyberArk created the CyberArk DNA tool to scan Ansible Playbooks to uncover hard-coded credentials on a continuous basis. CyberArk DNA is a free tool that provides you with a comprehensive report on all the hard-coded credentials in your Ansible Playbooks. See the diagrams below for an example CyberArk DNA report.
Secure your Pipeline and Playbooks
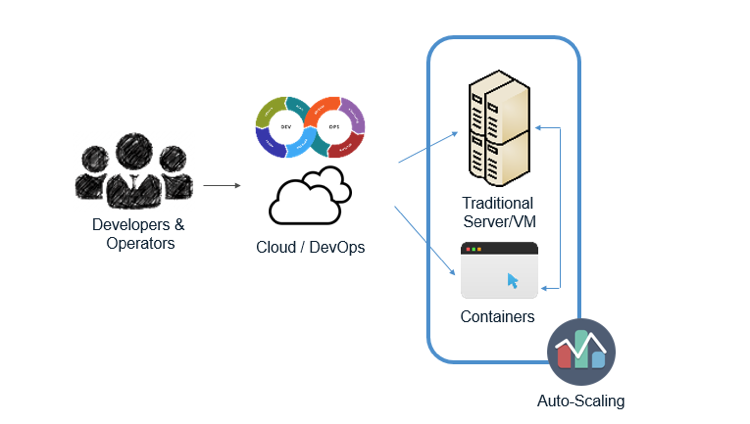
The CyberArk Conjur Ansible integration delivers automated off-the-shelf secrets protection throughout the DevOps pipeline. This integration secures the automated software delivery pipeline, allowing it to be efficient while deploying in DevOps environments. As with Ansible Playbooks, securing the secrets in the pipeline is essential to increasing the confidence of any artifacts created by the pipeline and making sure it is not vulnerable to attackers. Check out the diagram below to see how CyberArk Conjur secures your pipeline and Ansible Playbooks.
It’s also important to authenticate machines that need access to Ansible. The CyberArk Conjur Ansible integration provides a machine identity to authenticate hosts requesting access. This integration also helps you enforce least-privilege access to secrets and access credentials. This approach reduces the administrative power of the Ansible host and prevents it from becoming a high value target for attackers. To protect secrets, Conjur securely stores and automatically rotates credentials, as well as audits all access to them.
Comprehensive Security for Ansible Users
A user that has access to edit and run playbooks is a highly privileged user that needs to be protected and monitored. To protect your privileged Ansible users, you should:
- Enforce least privileged and granular access control via On Demand Privilege Manager (OPM)
- Monitor and track all user session activities with audit logs stored in a tamper-proof location with PSM Proxy (PSMP)
- Enforce least privileged and granular access control to your Ansible server. Privileged Session Manager or On-Demand Privilege Manager can secure remote command execution on nodes. They also support hybrid, multi-cloud or multi-segment networks.
By following all the steps above, and using technology like CyberArk’s Privilege Session Manager Proxy integration, CyberArk Conjur integration and CyberArk DNA, you can ensure that your Ansible deployments will be safe and secure.
Next Steps
- To learn more about how CyberArk Conjur can secure your DevOps pipeline with Ansible, watch this webinar. You can also get hands on with this demo in GitHub.
- If you want the CyberArk Ansible integration now, it can be found in Ansible Galaxy. You can also find the integration in the CyberArk’s Ansible Role Conjur and Ansible Conjur Lookup repos.
- Try the CyberArk Conjur Open Source tutorial.
Staff Writer
CyberArk uses a collection of staff writers and practitioners to support the DevOps Security.
