If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…
The Sword in the Darkness, the Watcher on the Wall
If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…

Mainstream technology enterprises widely use Kubernetes. It’s an extendable, lightweight, open-source container orchestration platform. This popular platform has an ever-expanding…

Editor’s Note: Please be aware that K3 is not officially supported on Conjur and the contents of this tutorial are…

Maintaining secrets in a secure way is an important — though often overlooked — aspect of security. DevOps security often…

Conjur controls access to secrets using role-based access control (RBAC). We cover this in detail in Policy Concepts, but, to…

Almost every application needs to deal with secrets in one way or another, to authenticate with a backend database or…
Centralized secrets management addresses important DevOps security attack vectors such as secret sprawl and security islands, but it could help introduce…

Since our first release of the Conjur Open Source Suite (OSS) aimed at helping development teams make the most of our secrets management…

Software and infrastructure architecture are quickly evolving into cloud environments. With this migration, Infrastructure as Code (IaC) is melding with…

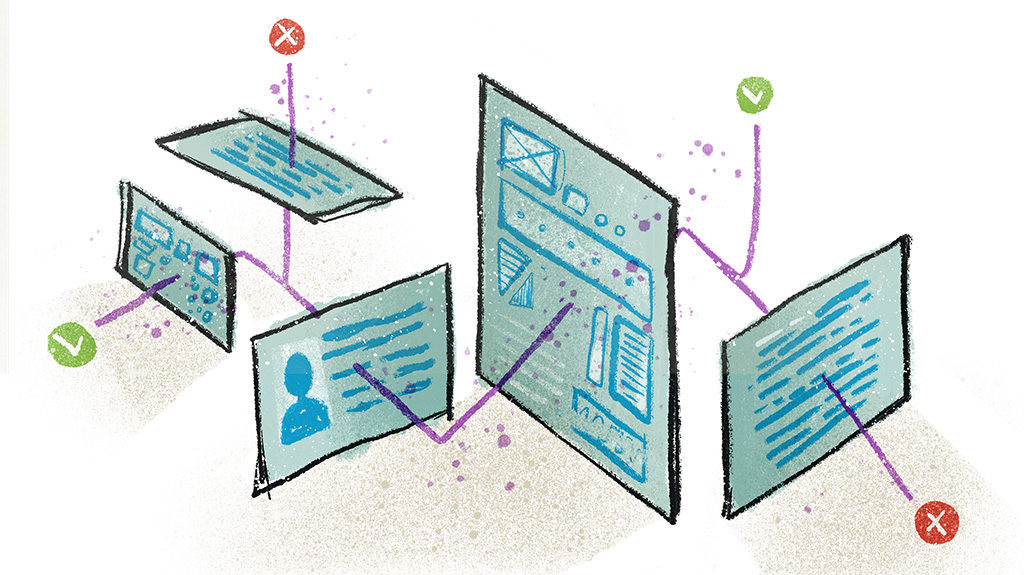
Application Security Overview Good application security (AppSec) prevents unauthorized access and modifications to apps by controlling access to sensitive information…

One concept that doesn’t always come to mind when we think of automated application testing is secrets management. That being…
Kubernetes is a great orchestration tool for your containerized applications and Amazon’s Elastic Kubernetes Service (EKS) provides an easy way…

In many ways, on-call duty and secrets management might seem to occupy pretty different parts of the IT universe. When…

Secrets management is a critical problem for developers, especially for teams adopting DevOps practices. Until recently, it was the IT…

Machine-to-machine communication is very important in today’s business-in-the-cloud. A lot of credentials and secrets are used and shared by non-human…
Chaos engineering, which aims to make software-based systems as resilient as possible in the face of unexpected error conditions, is…
We’re living in a cloud-native world, and the tools and strategies that worked in the pre-cloud era often no longer…

As organizations of all cuts and sizes are migrating to the cloud, there is a need to risk-assess the outcomes…
Developing modern web applications in the cloud nowadays is more streamlined than ever. This is true because many external vendors…

Microservices are taking the world by storm, and the movement isn’t showing signs of slowing down any time soon. The…

Over the past decade, software development and information technology operations have become more integrated, spawning a new approach, commonly called…

In this article, we’re going to talk about the problems surrounding authorization for your AWS account. We’ll define what those…

The Internet of Things, or IoT, is what allows us to take the power of computing beyond desktops, servers, and…
Back when I first became a programmer, it was a common practice to include database credentials right in the code…

I was really excited to attend the Cloud Native Computing Foundation’s (CNCF) KubeCon + CloudNativeCon Kubernetes conference in Seattle. I…

The Secret Zero Problem I have talked to a number of security conscious professionals across a wide range of…