If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…
The Sword in the Darkness, the Watcher on the Wall
If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…
Conjur Open Source is a robust secrets management tool to manage, audit, and control access across multiple platforms. Let’s explore…
The Ansible Tower integration with CyberArk Conjur allows users and administrators to map sensitive credentials (like passwords, SSH private keys,…

Secrets management assists organizations in authenticating applications and checking clients before allowing them to access sensitive information, systems, and services….

No matter their occupation, nobody likes to do the same set of tasks repetitively — especially when automation is an…
The Conjur OpenAPI is a language agnostic API description standard that allows for both human and machine users to investigate…

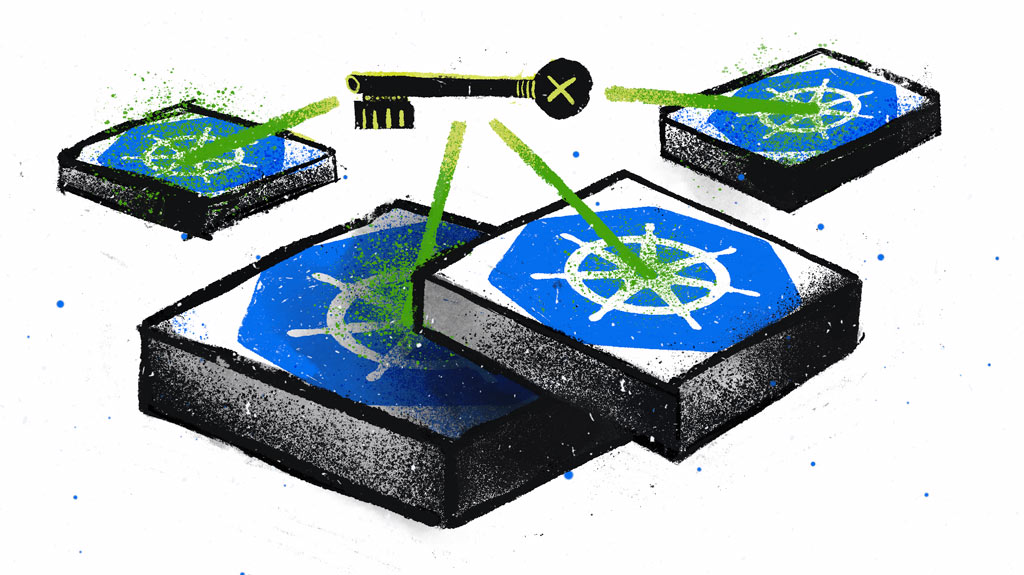
Red Hat OpenShift is a Kubernetes-based platform for container orchestration. OpenShift differentiates itself from Kubernetes through features such as tight…
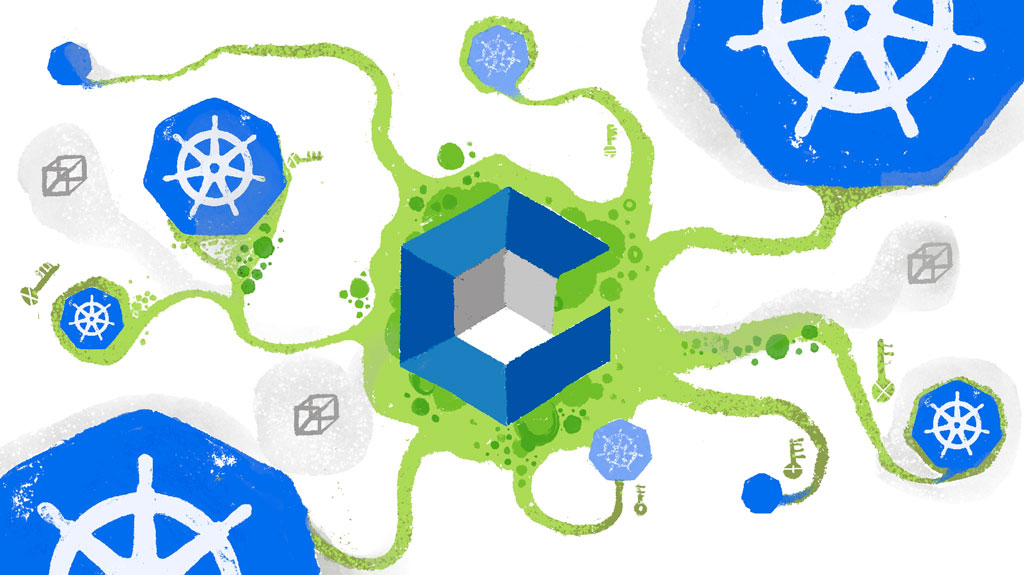
By default, Kubernetes uses Base64 encoding to store information such as application credentials, keys, and certificates. Unfortunately, this Base64 encoding…
Knative is the de facto standard for running serverless workloads in Kubernetes. But what do you do when your Knative…
Businesses need to provide flexible access to services that scale efficiently while always protecting customer data. Technologies like microservices and…

In recent years, there is a trend toward so-called low-code and no-code platforms. While no-code platforms often appeal to businesses…

In today’s world of cloud environments, deployments often use infrastructure as code (IaC). IaC deployments use a domain-specific language (DSL)…

With technology becoming a central part of our daily lives, we need to keep information safe from an equally rapidly…

Cloud-native applications use resources available to them online, on a public cloud platform, or hosted on-premises. IT teams apply policies…
Most secrets management solutions rely on a master key or “secret zero” that can unlock other credentials. The problem is…

In the first and second articles of this series, we discussed managing the information needed to build and test applications….

The first article in this series discussed the value of integrating Conjur with Jenkins. This article focuses on implementing Conjur…
Handling secrets in cloud-native environments is a challenge for many organizations. Virtually any application requires some sort of secret, such…

Jenkins is a versatile platform for implementing continuous integration and continuous delivery (CI/CD) processes to develop applications. Using plugins, Jenkins…
Kubernetes is a popular choice for microservices because it provides scalable, portable, efficient deployment and reduces most DevOps overhead. Generally,…

Maintaining secrets in a secure way is an important — though often overlooked — aspect of security. DevOps security often…
Managing cloud infrastructure isn’t a simple task at the best of times. From initial provisioning and configuration to maintenance and…
Conjur provides excellent policy and command examples. The Getting Started with Conjur guides and Conjur Documentation should be your first…
Secrets Management Policy Management through Java Spring Boot and Conjur The primary task of a secrets management administrator is to…
DevOps teams rely heavily on their CI/CD configuration tools to automate processes, accelerate delivery timelines and innovate at high velocity….
Organizations are migrating and deploying new workloads in cloud environments much more rapidly than ever, instead of expanding traditional on-premises…
Learning is fun, and the best way to learn is through hands-on exercises. That’s why Conjur provides some tutorials to…

The Conjur REST API is now available as an open-source OpenAPI definition. This effort creates new avenues for API exploration,…
Secret management is essential for ensuring an organization’s cybersecurity. In this era, when users share valuable information with service providers,…

Lambda functions are a great way to build a microservices application without the need to provision or manage servers. You…
Building a secure AWS environment requires applying security principles and guidelines around the way credentials and sensitive information are shared…

Conjur controls access to secrets using role-based access control (RBAC). We cover this in detail in Policy Concepts, but, to…

In today’s day and age, it’s hard to overstate the importance of data. Every day organizations throughout the world build…
Centralized secrets management addresses important DevOps security attack vectors such as secret sprawl and security islands, but it could help introduce…

Software and infrastructure architecture are quickly evolving into cloud environments. With this migration, Infrastructure as Code (IaC) is melding with…
Kubernetes is a great orchestration tool for your containerized applications and Amazon’s Elastic Kubernetes Service (EKS) provides an easy way…

After much hard work, our team is pleased to announce the release of our new v3 of CyberArk/Conjur Puppet module…

In many ways, on-call duty and secrets management might seem to occupy pretty different parts of the IT universe. When…
One of the most important aspects of today’s cloud infrastructures is secrets management. There are many possible solutions, all of…

Secrets management is a critical problem for developers, especially for teams adopting DevOps practices. Until recently, it was the IT…

When we talk about Secrets Management and handling secrets, we ought to think about all the users of the system…

The role of the developer has changed a great deal in recent years. Application architectures now include microservices, distributed systems,…

Machine-to-machine communication is very important in today’s business-in-the-cloud. A lot of credentials and secrets are used and shared by non-human…
Some GitHub repositories don’t just contain code – they contain passwords, API tokens, and credentials. The worst part? These are…
I would like to take a moment to talk about the exciting work our team has done to improve the…
Online demos and tutorials are a great way to introduce Kubernetes-native applications to potential users and collaborators. Often, however, these…
We’re living in a cloud-native world, and the tools and strategies that worked in the pre-cloud era often no longer…

Secrets sprawl, as the name suggests will grow out of control and become a tangled mess when it is not…

As organizations of all cuts and sizes are migrating to the cloud, there is a need to risk-assess the outcomes…

Microservices are taking the world by storm, and the movement isn’t showing signs of slowing down any time soon. The…

Over the past decade, software development and information technology operations have become more integrated, spawning a new approach, commonly called…
When you are developing an application, there are some important things that should not fall into the hands of strangers….

The Internet of Things, or IoT, is what allows us to take the power of computing beyond desktops, servers, and…
Back when I first became a programmer, it was a common practice to include database credentials right in the code…

The Secret Zero Problem I have talked to a number of security conscious professionals across a wide range of…